If you experience any difficulty in accessing content on our website, please contact us at 1-866-333-8917 or email us at support@chicagovps.net and we will make every effort to assist you.
Setting up your own Git server is not just to appease your geeky side, in today’s environment, it is critical. Gone are the days when your resume was all that was looked at. Companies looking to hire you google your name, stop by your GitHub repos and look at all your projects. You can no longer afford to have projects that you started but left it untouched many years ago. (Don’t say much for commitment eh?)
Setting up a private Git server with closed repos lets you test your ideas in sandbox before unleashing them on to the world. This article will cover setting up your own Git server with a nice Front end UI.
Git servers can co-exist on your existing VPS, even if it runs a well visited website. There is no processing happening at the server unless you commit and push from your local copy. Therefore we will look for a lightweight Git server application that is better than just a command line interface
Gogs is a self-hosted git server written in Go and demands lesser in terms of hardware than Gitlab. It supports both SSH and HTTPS modes of operation. Best of all, it has a web interface that will make life easier for those “just-one-line-change” moments. If you are a GitHub fan, you will hardly notice the transition to Gogs.
We will install Gogs on a 512MB VPS. If you are using MySQL (our article covers SQLite) as the backend, you should probably go for a 1GB RAM VPS
As with all installations, we start by updating our current system to the latest and greatest versions of installed packages (all the below steps are carried out as root)
![]()
On Ubuntu,
Install Git from your corresponding repository
We need to create a user that runs Gogs and will have complete control over the files & repository contents. Let’s call this user git
Navigate to /home/git. We will download the latest version of gogs as a binary from the gogs.io website (https://gogs.io/docs/installation/install_from_binary). At the time of writing, the version was 0.11.53
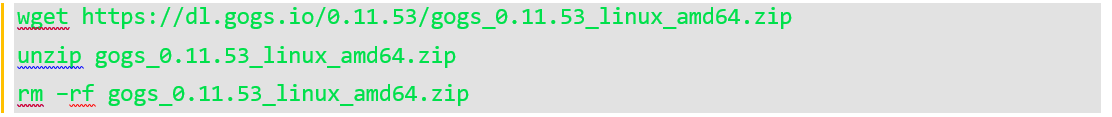
Now gogs is in /home/git/gogs folder. You are almost ready to run Gogs.
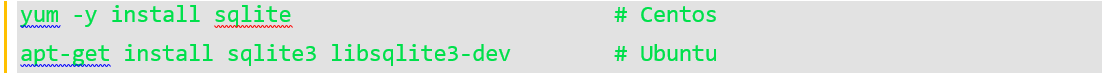
If you are wondering about SQLite3, by default, most Linux OS installations have SQLite3 installed. If not, install through these commands
Now back to the /home/git/gogs folder. Type ./gogs web
Gogs server begins and is now accessible on port 3000. You will see a bunch of messages, look out for [ INFO] Listen: http://0.0.0.0:3000
Since it is 2018 and no one uses http anymore, we will setup https for the server and also make changes to run gogs as a service. However, we will complete setup of gogs first. Navigate to the URL http://[server-ip]:3000, you will see the setup page. In this page, under Database Settings, choose SQLite3 and the absolute path to the gogs db. We will use /home/git/gogs/gogs.db
Under Application General Settings, enter the application name, the path to the repositories (absolute path please). Run user is git (the user we setup earlier). Enter the domain name of the server, a sub-domain URL also works here. If you haven’t setup CNAME records, you could enter the Server IP.
Unless you are running SSH on a different port, the next field SSH Port will remain 22. We will leave the HTTP port to 3000, change the application URL to match your domain name (or your Server IP). Include the port number 3000 after the URL. For e.g., the Application URL field could look something like this
![]()
The next section in settings is “Optional Settings”. Jump right into Server and Other Settings. Disable Self-registration and Enable Require Sign In to View Pages. After all, you are looking for a place away from prying eyes to carry out private development.
Lastly, create your admin account. Generate a random strong password, email is optional and click Install Gogs. If all is well, you should be able to log in to your dashboard.
Even if you are the sole repo user, it is important to encrypt the traffic between your local repo and the one you just created. Being the cost-efficient folks that we are, we will get the job done with Let’s Encrypt’s free SSL certificates.
Let’s Encrypt installs as certbot, available for all Linux flavors. Before we proceed though, you have to ensure that the application URL (gogs.thisexample.com, in our case) points to the server’s public IP. Note that certbot checks both the actual URL and the URL prefixed with a www, so when you are making DNS entries, add the www.<application-url> entry as well. Port 80 must be publicly accessible for certificate issuance, so if it is firewalled off, make sure to turn it off temporarily. Stop the gogs application that you started earlier (Ctrl+C works)
Ubuntu
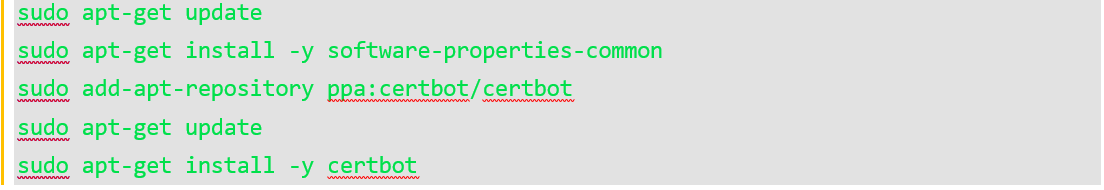
Centos
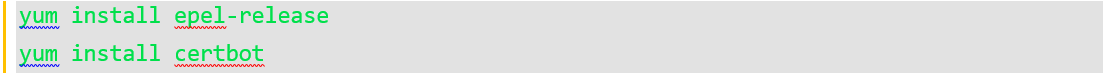
Certbot is available via the EPEL release for Centos. We will enable it and then install certbot
To issue a certificate, run the following command replacing the URL with your application URL
![]()
Answer all questions onscreen and your certificates are issued. The public and private key pair are located at /etc/letsencrypt/live/gogs.thisexample.com/
We will create a link between this folder and the gogs folder so the application can access this.
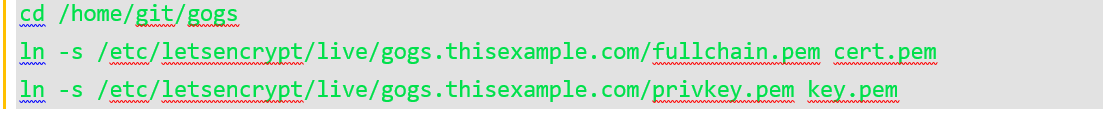
Give the user git access to these files
![]()
Now, we will change gogs application settings to run over HTTPS
![]()
Search for [server] and add these lines
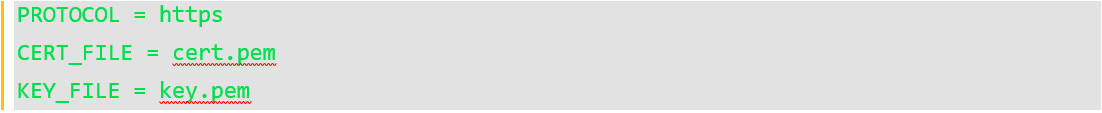
Also lookout for the variable ROOT_URL, it should be https
We are not completely done. The last step is to make sure Gogs keeps running even after you close your SSH session and after server reboots. This is relatively simple as Gogs pre-ships with configuration files for running Gogs as a service
Ubuntu

Centos
The service is now enabled and you are all set.
If you followed the above steps, you have a functioning Git Server. Go ahead, create that tic-tac-toe-meets-rubiks-cube project that you had always wanted to code. When it is released, let us know. We would love to play.
Certbot instructions for various flavors and web servers – https://certbot.eff.org/all-instructions
